Legacy systems are vulnerable to attacks, failures and other unexpected operational interruptions, so why have they not been replaced? Organizations either fail to understand the risk or have not replaced out-of-date systems because of budget constraints, IT priorities or the complexity of replacing an indispensable component of their enterprise. Consequently, these vulnerabilities cost businesses time, money and could result in complete system failure.
The Legacy Problem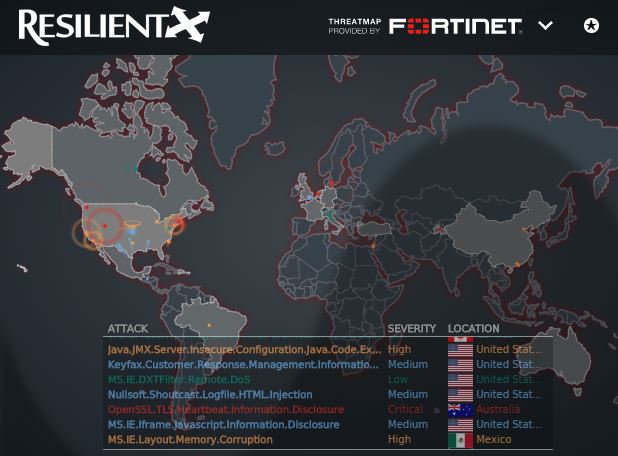
Before buffer overflows, SQL injections and even the Internet, writing an application included nothing more than coding functionalities as sparsely and effectively as possible. The code was built for stable and efficient operations without security in mind. Unfortunately, these applications are still supporting critical infrastructures within the energy, medical and financial industries and are at risk for a major security breach.The vulnerabilities that lie in hard-coded and default passwords represent such a security threat that the U.S. Department of Homeland Security warned organizations that unless they change passwords, hackers could easily steal default passwords and "identify internet-connected target systems".
According to DHS: “Passwords are found in compiled lists and product documentation readily available on the Internet. Attackers knowing passwords can gain network access to a system and log in, usually with root or administrative privileges.” In particular, legacy systems typically have a variety of backdoor accounts providing access to important databases that attackers could compromise.
Patching Legacy Systems--Does It Work?
Patches are issued to protect vulnerable legacy systems but they are often not applied. Testing of the patches by IT is difficult and the stability of the application is so critical to its operation that many companies never apply necessary patches to old network systems.The problem feeds on itself as each time an upgrade or patch is released, it becomes more expensive and difficult to implement the next one. Eventually, a neglected, outdated system falls into technological debt--a situation that makes it too expensive to save. Or, if the system is compromised, the organization ends up in disaster mode.
Protecting Legacy Systems in the 21st Century
Attackers focus on easy prey. Organizations need to rethink their strategy when it comes to legacy systems by concentrating on securing their digital interfaces and data. Software security experts strongly urge companies to enlist the assistance of network security professionals to update, patch and reinforce their systems to prevent potential breaches.Systems integration experts like Resilient work with organizations to secure current applications and build a strategy to create a new infrastructure to replace legacy applications. Resilient works with best in class technology, such as Fortinet, to address each organization's unique requirements and tailor solutions to their needs. Check out FortiGuard Threat Intelligence in Action!